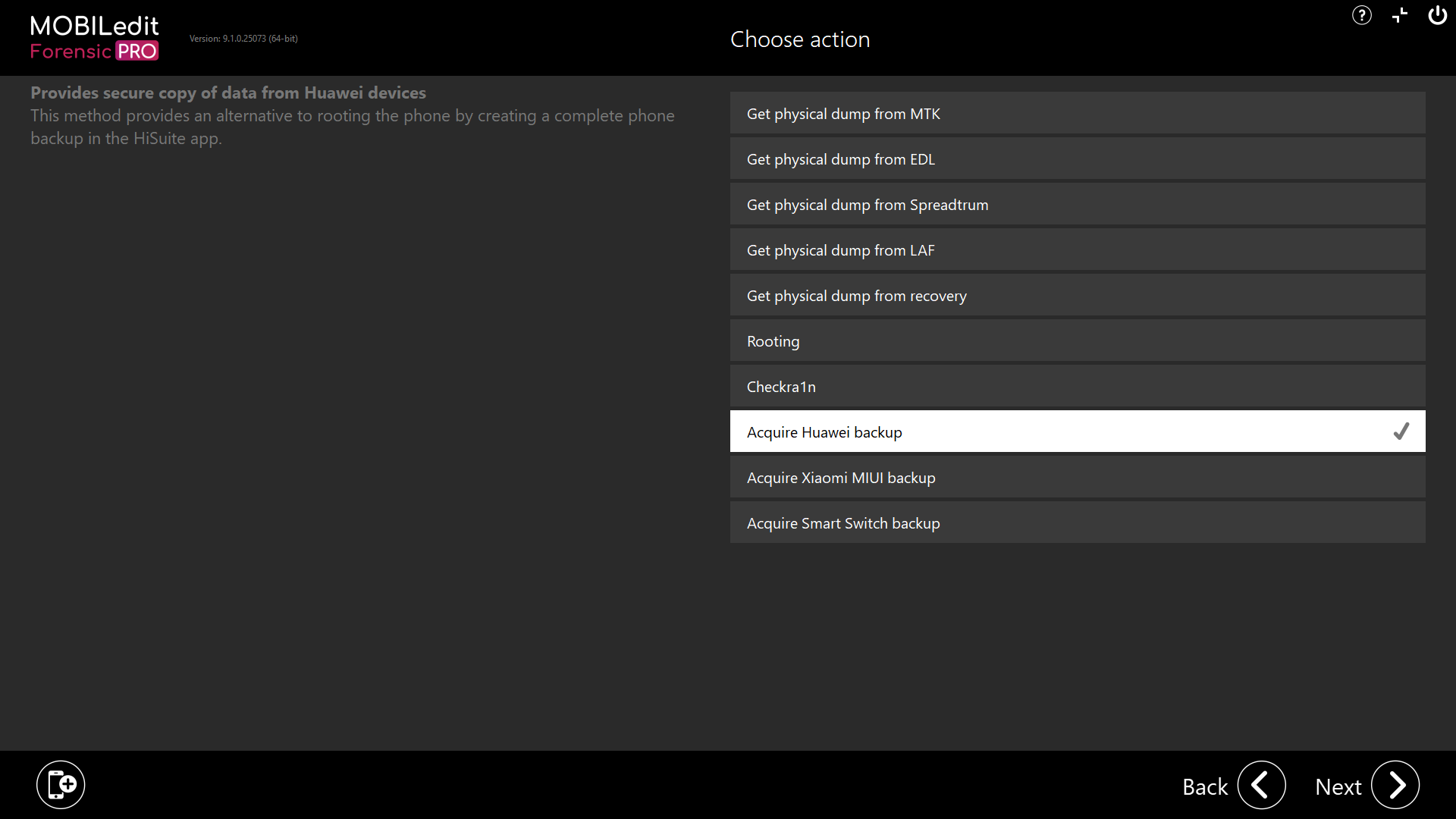
Within the security bypassing options you will see options for acquiring backups from connected devices.
The reason this has been included here is that in some circumstances, depending on make, model and OS version, it is possible that you may get additional data over and above what you would get from a logical extraction.
Sometimes a backup will export application data that might not normally be accessible with a logical extraction due to application package permission security. We do not have a specific list of devices yet, have included it in security bypassing as another option.
The following backup types are supported for direct acquisition from a connected device:
-
Acquire Huawei backup
-
Acquire Xiaomi MIUI backup
-
Acquire Smart Switch backup
If you do not have a connected device and, you have seized a computer containing a phone backup as part of your investigation, you can import the backup for extraction and analysis. More details can be found in the user guide pages under the heading Import data.
It is always advisable to use dedicated forensic software to match the type of device, image or files that you wish to examine. So for mobile device-related files, you should use MOBILedit Forensic. For computer-related devices, images and files, you should use forensic software compatible with that platform.

