Malware Detection in MOBILedit Forensic
MOBILedit Forensic features a powerful malware detection module that utilizes the industry-standard YARA engine to scan Android and iOS devices — including physical images, backups, and supported imports like UFDR files — for known indicators of malware.
How Malware Detection Works
The malware module uses a collection of YARA rules that define specific data patterns which may indicate the presence of malicious software. MOBILedit Forensic applies these rules to the extracted data, scanning all accessible files on the device for matches. When a file matches a rule, it is flagged as potentially harmful and listed in the final report.
Note: The rules database used by MOBILedit Forensic is based on both our historical malware database and a curated collection of publicly available rules used by malware analysis professionals. These are distributed in the form of a package and updated via Live Updates.
Custom rule sets can also be used by the investigator.
Custom YARA Rules
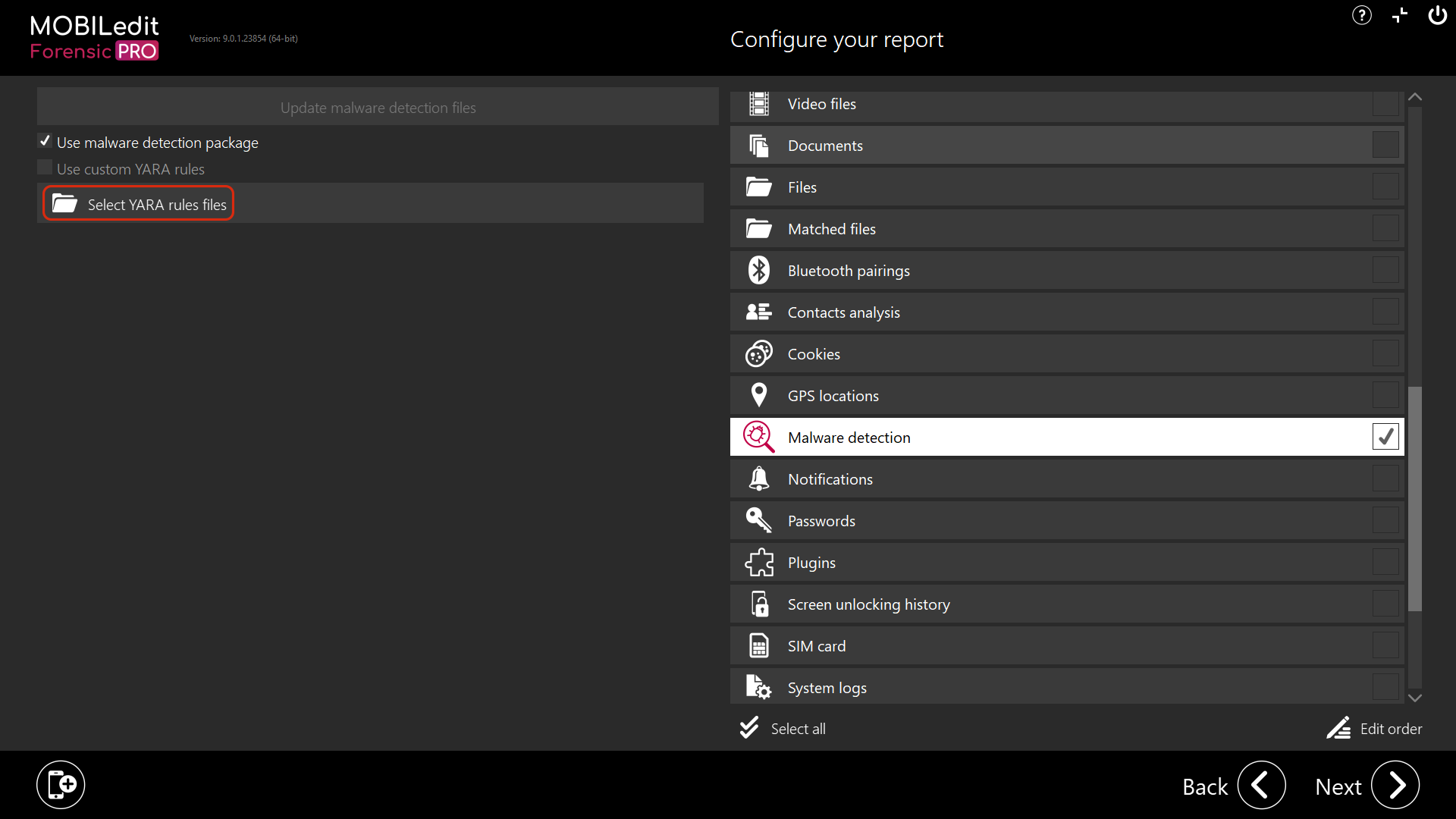
You may import your own .yar or .yara rule sets using the “Select YARA rules files” option in the interface. After selection, enable the "Use custom YARA rules" option to activate them.
-
Both the MOBILedit rule set and custom rule set can be used together.
-
It is advised to test custom rules in advance to minimize false positives.
Scope of Scanning
-
All files accessible from the extraction are scanned, including those from system partitions, app data, and user storage.
-
Rooted (Android) or jailbroken (iOS) devices allow for broader access, improving the likelihood of identifying malware.
-
Unrooted or non-jailbroken devices may result in limited malware detection, particularly at the logical level.
Tip: Consider running the malware scan as a separate task to reduce analysis time for full-content extractions. Enabling malware detection will increase the overall processing time.
Results in Reports
-
Identified files are listed in the report along with APK metadata and additional information.
-
The flagged files are not executed, removed, or modified.
-
This preserves the integrity of the connected device and ensures no changes are made.
-
If no malware is detected, the report will explicitly state that the Malware Detection module was executed and that no threats were found. This confirmation ensures transparency and verifies that the module ran successfully as part of the analysis.
Forensic reports are intended to assist investigator review — not to act as an antivirus system that can quarantine or neutralize threats.
Once a file is flagged, the investigator must evaluate it:
-
What is the file?
-
What app does it belong to?
-
Is it harmful, suspicious, or simply intrusive?
Due to the variety of malware types (e.g., spyware, adware, unwanted apps, backdoors), further manual research or reverse engineering may be required to classify the behavior of flagged files.
False Positives
False positives may occur. If a rule partially matches benign content, a non-malicious file might still be flagged.
-
iOS: False positives usually occur due to partial-string matches within the rule set.
-
Android: Some manufacturer apps may exhibit behaviours similar to malware (e.g., stub apps or update backdoors).
If you identify a consistent false positive, we encourage you to report it to the MOBILedit Forensic team so we can evaluate and adjust the rule base if appropriate.
iOS-Specific Considerations
-
Only Pegasus malware is currently detectable on iOS.
-
Indicators are found via links and artefacts stored on the device or in backups.
-
Jailbreaking is recommended for maximum visibility, but not required.
-
Evidence of Pegasus may also be detected in iTunes backups — consider running the malware module on these as well.
Android-Specific Considerations
-
Rooted devices yield the best detection coverage.
-
MOBILedit Forensic can detect a broad spectrum of Android malware.
-
Some legitimate apps may behave similarly to malware — always verify flagged results.
Legal and Investigative Considerations
Ensure malware detection falls within the scope of your legal authority and is relevant to your case. Scanning user files for malware must be justifiable under the warrant or consent that grants access to the device.
Also, consider disabling your PC’s antivirus during extraction to avoid deletion or interference with potential malware samples — which would otherwise not be included in the final report. You can also exclude your report output folder from being scanned by antivirus.
Summary
The MOBILedit Malware Detection module is designed to support forensic investigators in identifying potentially malicious files. It is a passive, non-destructive scanner powered by YARA, customizable, and suitable for use in both standard and advanced forensic workflows.
While false positives may occur, the module provides an essential layer of insight into device activity and suspicious content, especially when paired with full file system access and experienced analysis.
Report example
Malware detection - PDF Demo Report - MOBILedit Forensic PRO 9.0.1.23854 (1).pdf

