EDL - Get Physical dump from EDL
Intro
The EDL method extracts a physical image from phones that use Qualcomm chipsets, without root access and bypassing the lock screen. Using the Emergency download mode, MOBILedit Forensic accesses the phone memory through the System on Chip (SOC) using a device-specific firehose loader programmer file.
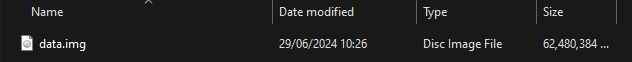
Please note that the physical image is as big as the full phone storage.
Approach
The EDL method can be accessed via:
A live-connected device and choose“Next”.
Security bypassing option on the “Connect devices or import data” screen:
By model
By chipset
By method
“Connect device” option on the “Connect devices or import data” screen
To read more about these options, visit the “approach” page.
Emergency download mode (EDL)
EDL method is a way of extracting physical images from phones with Qualcomm chipsets. This option does not require the phone to be rooted and works on most Qualcomm-equipped devices once the device is in Emergency download mode.
Every device has a specific way to enter EDL mode:
Handset key combination
EDL cable
Test points (See image below)
ADB command “adb reboot edl”
Fastboot command “fastboot reboot edl”
When set to EDL mode, the device identifies itself as “Qualcomm HS-USB QDLoader 9008” in Device Manager.
You must have the “Unlocking drivers” installed for Windows to communicate with the device in EDL mode.
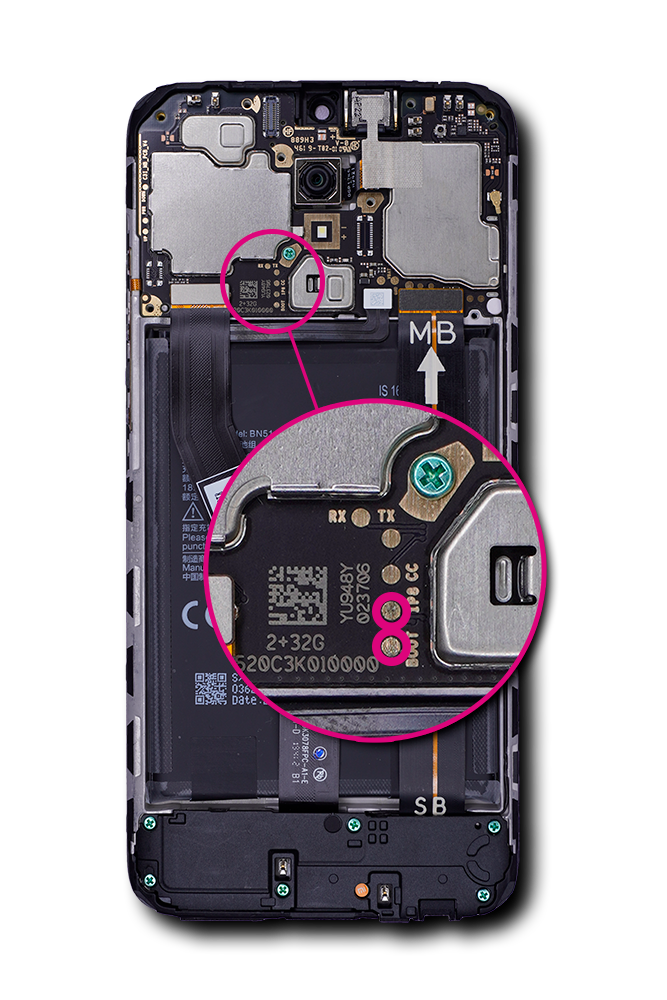
Xiaomi Redmi 8A
When using the “By model” option it may be possible to see a photo detailing the location of test points for a device if the test points are known to us.
Where it is known to us that shorting of the test points is required to enter EDL mode and, we have previously tested that specific device, we have provided graphical instructions within the software to assist you. Below is an example of the location of the test points on a phone's printed circuit board assembly.
How to
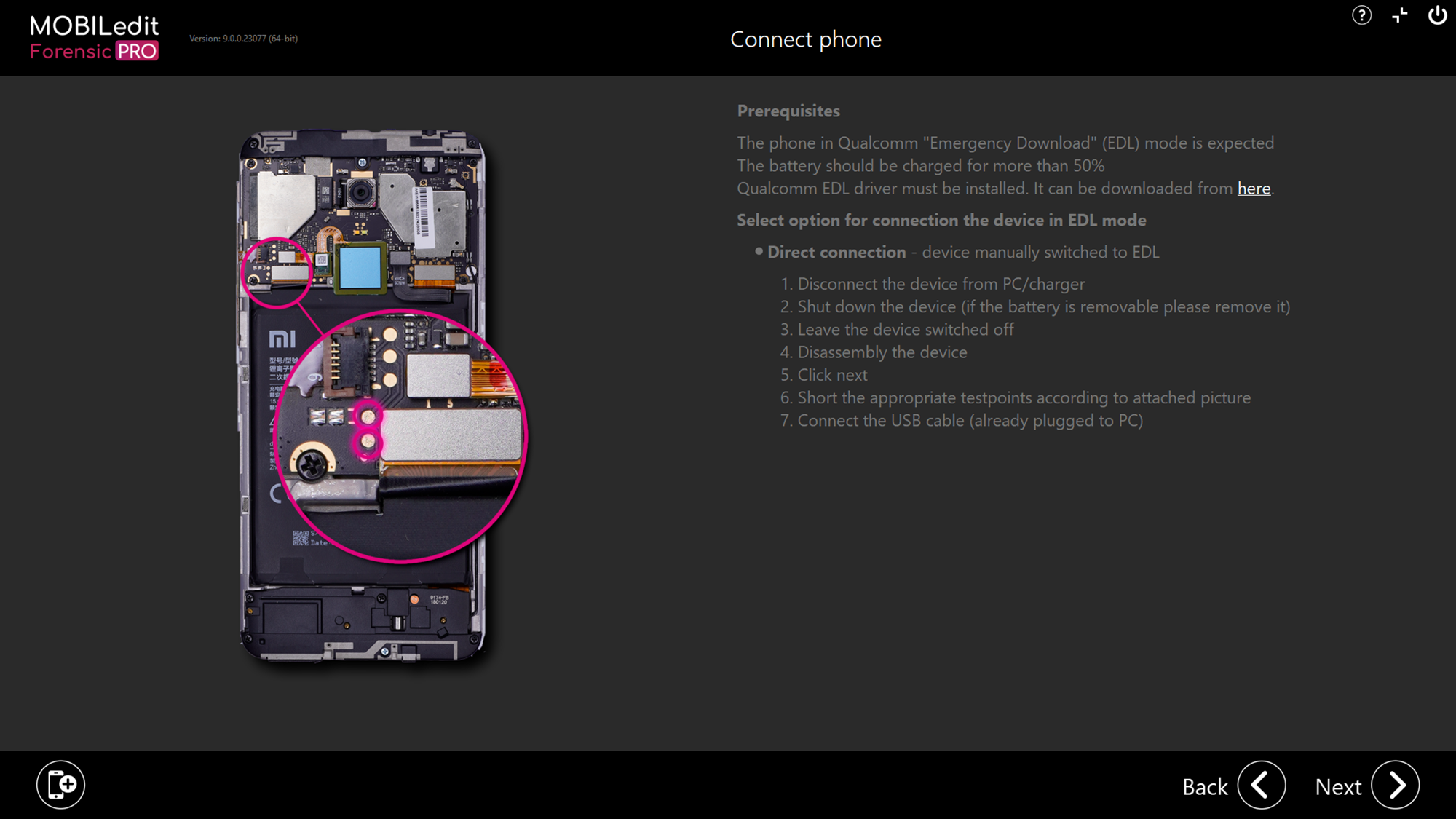
Whatever “approach” you choose to access the EDL method, you will ultimately reach the screen below where there is a reminder of the prerequisites, connection steps and how to enter EDL mode:
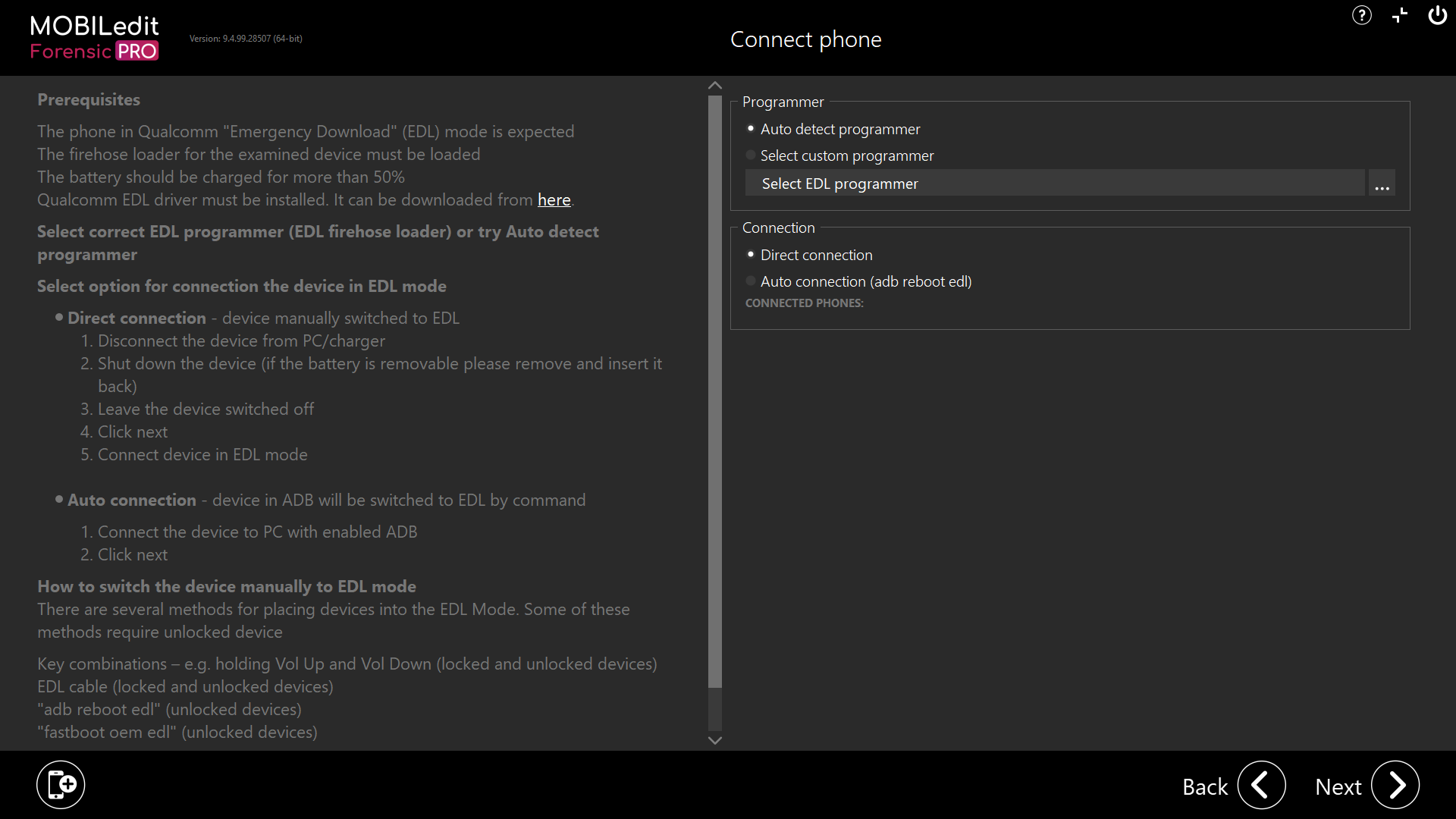
If MOBILedit Forensic does not have a preinstalled programmer for your device, you can try to search for a programmer yourself on the internet.
Once found, choose "Select custom programmer" and import the programmer to MOBILedit Forensic using “Select EDL programmer” and click the three dots. Then after selecting the file and clicking “Next”, connect the phone in EDL mode, if the programmer is correct, a physical image will be extracted.
We recommend looking for a programmer for the phone you are investigating however, a programmer for a similar phone or chipset may also work.
There is no risk of data loss by trying different programmers.
Alternatively, you can select “Auto detect programmer” and MOBILedit Forensic will choose some of the programmers that could work. If MOBILedit Forensic finds a suitable one, a physical image will be extracted.
Enter EDL mode through ADB command
It is possible to enter EDL mode through ADB command directly from within MOBILedit Forensic. The device must be connected with USB debugging enabled to communicate via ADB.
On the "Connect phone" screen, select "Direct connection (adb reboot edl)" in the "Connection" section. Then connect a live phone with ADB enabled. Click next and your phone will boot into EDL mode.
Using ADB command "adb reboot edl' will not work with Xiaomi’s MIUI 8.0 or above.
In some cases the fastboot command "fastboot oem edl" might work, you may need an unlocked bootloader.
To show the method in full, we will use a live-connected device and select “Next”
SCREENSHOT
MOBILedit Forensic automatically detects the connected device has a Qualcomm chipset and offers the method “Get physical dump from EDL”. Select and then click “Next”
SCREENSHOT
Upon reaching the Connect phone screen, carefully read the instructions, choose your options for programmer and connection if required, prepare the device, then when you are ready to connect, click “Next”
SCREENSHOT
You may have to try several methods to get the device into EDL mode.
If it is possible to use this method with the connected device, the physical will be extracted.
SCREENSHOT
Once complete, MOBILedit Forensic will attempt to automatically load the physical image for a logical extraction and analysis of the newly extracted physical image.
SCREENSHOT
If the physical image uses encryption, it will fail to load as the HW keys cannot be extracted with MOBILedit Forensic PRO. To load and decrypt the physical image, you must use MOBILedit Forensic ULTRA.
SCREENSHOT
When the physical image is acquired using PRO and is encrypted, it would still be possible to connect the device with ULTRA in the future, extract the keys, load the original acquired physical from PRO, and decrypt the image.
The physical image will be saved in the report output folder:
Other
To identify what type of encryption the device is using, please visit this page:
If you are using EDL method and your device is not supported through live connection or “By model”, you can try the “By chipset” approach for the same or a closely matched chipset. This method is safe and will not harm the data or device itself.
Alternatively, search the internet for a firehose loader/programmer file. Good places to look for test point locations and programmer files are; paid sites, YouTube and other video channels, XDA Developers forum, Githib and the Digital Forensics Discord forum.
Additional sources
Additional articles about EDL and advanced methods:
https://alephsecurity.com/2018/01/22/qualcomm-edl-1/
https://www.xda-developers.com/exploit-qualcomm-edl-xiaomi-oneplus-nokia/
