MOBILedit Forensic performs mobile phone, smartwatch and cloud content extractions and is used by professionals in law enforcement, the military, government organisations, and also in the corporate and private sectors. By connecting a phone via USB cable, Wi-Fi or Bluetooth you can perform individual examinations of most mobile devices and generate reports in multiple formats (PDF, HTML, Excel, etc.) for a variety of needs.
MOBILedit Forensic can retrieve messages, call logs, pictures, contacts, apps, calendar events, emails, passwords, media, file systems, deleted data, and much more. You can even select specific data which you want to extract from the device.
Before you begin
For the best possible experience, we recommend taking a look at the minimum system requirements.
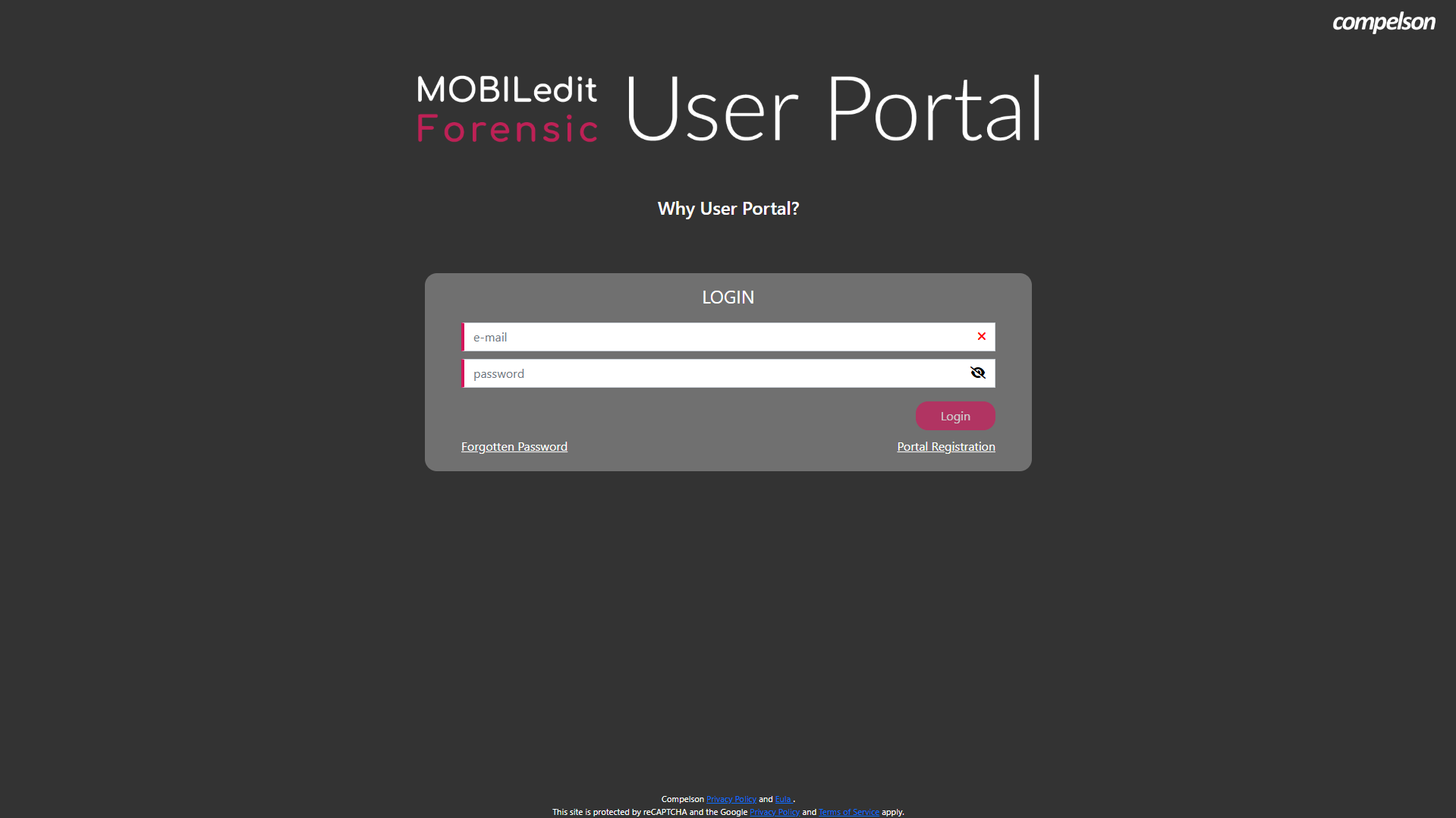
Register in the User Portal and then download and install MOBILedit Forensic if you haven’t already. Activate the software with a valid license.
The digital key version of MOBILedit Forensic is not compatible with the dongle. For the dongle version please contact our technical support.
All versions of MOBILedit Forensic can be run offline, including both the digital key and the dongle versions. However, an internet connection or, internet-connected computer, is required for activation and updates for both types of license.
The step-by-step installation guide is available in the video below:
MOBILedit Forensic Installation Guide
Before connecting the phone, be sure you have installed the necessary device drivers on your PC. You can download our Complete Driver Pack or select the required individual drivers.
When connecting an Android device with MOBILedit Forensic running on a 64-bit version of Windows, the device drivers provided by the manufacturer of the phone might be sufficient to allow a proper connection between the device and the software. If not, you might need to replace it with the universal ADB (Android) driver.
Connecting phones
Please read the device-specific pages for how to connect with a device.
Getting maximum including deleted data
While MOBILedit Forensic is a very powerful extraction tool and extracts practically all information available, advanced users looking to get even more information from the phone should first 'root' or 'jailbreak' the phone.
Android rooting is an important step that will allow maximum data and additional deleted data acquisition. If you cannot or do not want to root the phone, you can alternatively use one of the temporary root access methods or the Application Downgrade feature to find hidden and deleted data in certain supported apps.
For iPhone iOS devices, ideally, the passcode and iTunes backup password are required. Jailbreaking an iPhone can bypass several types of Apple prohibitions for the end-user, including modifying the operating system (enforced by a "locked bootloader"), installing non-officially approved applications via side loading, and granting the user elevated administration-level privileges (root access). You can also try to bypass the passcode on locked iOS devices with the Lockdown Files Method.
If you can’t find the information you require in this fully comprehensive User Guide, or if you have any questions regarding MOBILedit Forensic, please do not hesitate to contact our technical support team.

